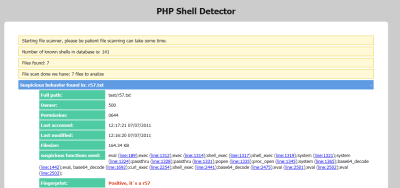
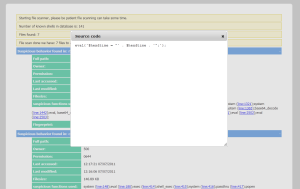
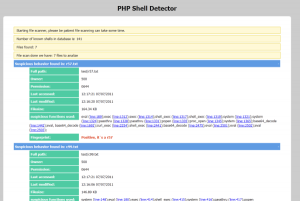
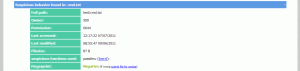
PHP Shell Detector is a php script that helps you find and identify php shells. It also has a “web shells” signature database that helps to identify “web shell” up to 99%. By using the latest javascript and css technologies, php shell detector has a light weight and friendly interface . The main features is that if you’re not sure about a suspicious file, you may send it to the websecure.co.il team. After submitting your file, it will be inspected and if there are any threats, it will be inserted into a “php shell detector” web shells signature database and the next time this file will be recognized positively.
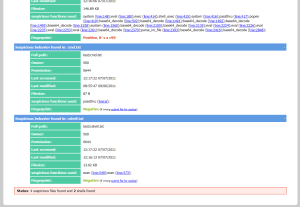
Screenshots:
Settings:
- extension – extensions that should be scanned
- showlinenumbers – show line number where suspicious function used
- dateformat – used with access time & modified time
- langauge – if I want to use other language
- directory – scan specific directory
- task – perform different task
- report_format – used with is_cron(true) file format for report file
- is_cron – if true run like a cron(no output)
- filelimit – maximum files to scan (more then 30000 you should scan specific directory)
- useget – activate _GET variable for easy way to recive tasks
- authentication – protect script with user & password in case to disable simply set to NULL
- remotefingerprint – get shells signatures db by remote
Number of shells in signature database is: 141
Demo: http://www.emposha.com/demo/shelldetect/
Download: https://github.com/emposha/PHP-Shell-Detector